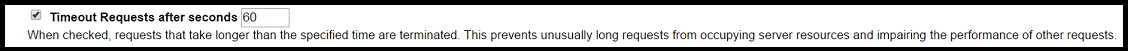
Enabling this setting will enforce a ceiling on request times. Any requests that exceed this duration will be terminated by ColdFusion.
It is highly advisable to enable this setting. Allowing ColdFusion to process a request for an indefinite amount of time can lead to hung threads (requests that will not complete). Given that ColdFusion has a finite number of threads available to process requests, enough hung threads can prevent ColdFusion from serving any requests. By setting this value, you are defining an upper limit on how long a request should process. Requests taking longer are removed.
Tip: If your site has certain pages that are allowed to exceed your defined maximum timeout, you can override this setting with the <cfsetting> tag on a per-page basis. This will allow you to set a reasonable timeout globally and ignore it when necessary.
According to Nielsen, after 8 seconds a website user is likely to click again or leave. The default setting of 60 seconds is therefore very high and serves as a starting point for your tuning effort. The best practice to right-size this setting is to enable Log Slow Pages in the debugging and logging section. Follow up by investigating all requests/pages running longer than 60 seconds in server.log. Refactor these pages and test.
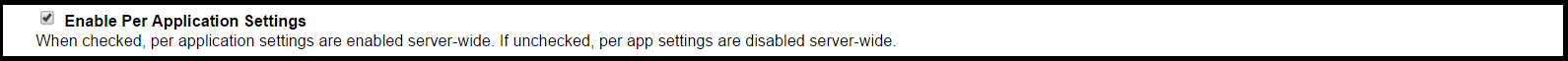
This setting can be useful if we want to allow developers to override some of the global settings declared in the ColdFusion Administrator. This is useful for installations where more than one site is bound to an instance of ColdFusion. Settings that can be overridden in your code include mappings, custom tag paths, and session/client timeouts. This setting is enabled by default.
![]()
Using a UUID for cftoken is a recommended security best practice if you are not using J2EE session management. It enforces a highly unique identifier per user with a significantly greater complexity than the standard numeric values for the client and session cftoken. The default is checked.
Tip: There are significant advantages to using J2EE session management over ColdFusion management of sessions. These are covered in more details in the Client Variables section of this guide.
Tip: Be sure to review our ColdFusion security recommendations to help secure your server.
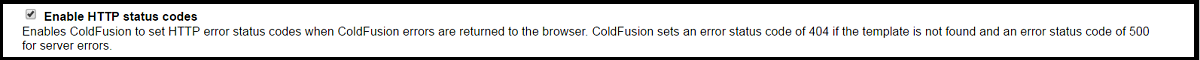
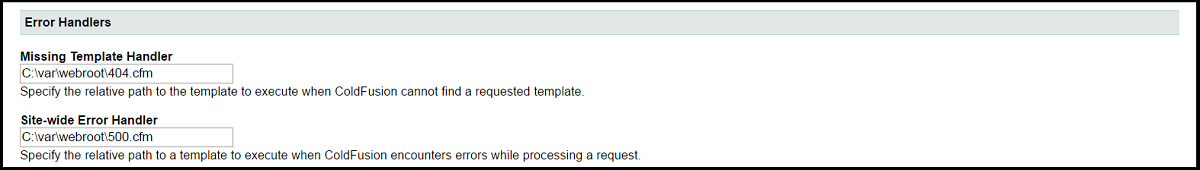
Having ColdFusion return known HTTP error status codes is helpful to search engines, proxies, and other automated systems that interact with your application. When a page is missing, this will cause ColdFusion to return a status code 404, which is universally recognized to mean “Page Not Found”. Similarly, when an error is thrown in ColdFusion, a status code of 500 will be returned. We recommend this setting be enabled in your production environment only. The default is checked.
This setting reduces the file size of the pages that ColdFusion returns to the browser by removing many of the extra spaces, tabs, and carriage returns that ColdFusion might otherwise persist from the CFML source file. This results in a smaller payload delivered to the browser for each page. If you are experiencing issues with broken JavaScript or CSS, it may be worth disabling this setting. Make sure your settings across your development, staging, and production environments are consistent so issues are not discovered in production. The default is checked.
When arguments are passed to a component method or user-defined function, ColdFusion will perform a validation to ensure that values of the right type are passed. If you pass an array as an argument that expects a string, ColdFusion will throw an error. Validation like this is helpful during development, but it comes at a slight performance cost. We recommend running with this setting enabled in your development and staging/test environments at a minimum. You may realize a performance benefit in production by disabling CFC Type Checking, however, it is typically negligible. The default is unchecked.
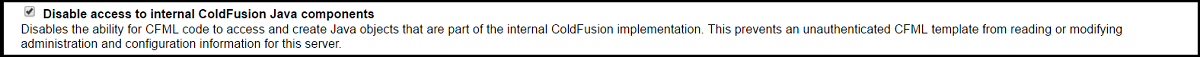
This setting restricts access to Java objects that provide core services for ColdFusion. As these can change with different versions of ColdFusion we recommend this setting be enabled (checked). This prevents an unauthenticated CFML template from reading or modifying administration and configuration information for this server. The default is unchecked.
![]()
By default, ColdFusion will force the keys of structures to uppercase, losing the original casing of the data. This side effect can hamper your ability to manipulate structures if the case of your keys has meaning. By enabling this setting, ColdFusion will maintain the defined case of keys in your structure. Our recommendation is to enable this setting, with the caveat that it may break existing code adapted to operate on all uppercase keys. The default is unchecked.